4 minutes
SHU CTF - Cyber Security Challenge
Yesterday I participated in a capture the flag event at Sheffield Hallam University organised by Cyber Security Challenge UK, it was a really interesting experience for my first in person CTF and I took away some points and advice for future CTF’s and things I need to look at and research. I arrived at around 9:30am and got myself signed in and then had some pre-game coffee (Very important before the CTF!!) once everyone started arriving eventually the hosts talked about the schedule for the day, the rules and what prizes are on offer.

We then moved towards the lab, and I found my team members for the CTF. Unfortunately my own university’s team from Abertay University were already full due to it being 4 members per team, so I was on a mixed team with students from SHU. After a brief introduction and creating our team name “Invaderz”, I got stuck straight into the challenges and worked on the miscellaneous and forensics challenges. The CTF was using a web app with different categories of challenges and each challenge represented a various amount of points.to score for the team, during the first few hours we was making progress and each of us scoring points which caused us to hold second place with Abertay University (Team Russel) holding first place.
We then had lunch after making some progress during the morning, and listened to a talk on WiFi leakage which was interesting to find out how much data our devices leak without us realising it, and the OSINT information that could be gathered.
After a quick charge up of energy and some more coffee (of course), we then made our way back to the hack lab and I started to work on the Wireshark forensics challenge, which seemed to be more challenging than I thought after spending half an hour trying to get the attachment decoded, and rebuilt from the pcap file. It did not help that Kali 2.0 was used in the labs and we could not update/install software due to the repo not working, and once I changed the sources to old kali 2.0 repo the software I needed would not install. So after looking into some more tools and commands I found some other software.
Then we were approached by staff to go and attempt to pick the lock for the lock picking challenge, with a chance to win more points. Off we went to attempt the challenge and was given a brief talk/demonstration on lock picking. After I tried to pick the lock, I managed to bend one of the tools… Which was not a good start, after one of us picked the lock we gave up and went back to the CTF to try and keep in the game and get to 2nd place. Time was running out at this point with only a few hours to go, so we was all desperately trying various challenges to try and rack up more points.
It then came up to the last ten minutes and I was trying as hard as I could to try and work out where the flag was in this pcap file, at this point we was still third which was not so bad. However… it then came to the last two minutes and one team had an ace up their sleeve and submitted a few flags which brought us into forth place with a 30 points difference.
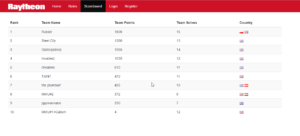
And that was it! A spectacular day, I learned loads and got to work with like minded people. It was also nice to see our university came first place (Shame I was not on that team!!). After speaking to other teams once it finished, it seemed I was looking in the wrong place in the pcap file, and actually had to login to an email and download the flag and not trying to download a attachment from the pcap file, which is why it was not working.
I will certainly be back next time!!